Impersonation is used to test changes in system configuration settings and in access rights. Impersonation is also used to demonstrate the implementation of automated processes in different roles.
Two following parties are involved in the impersonation process:
If a user has the impersonator role, they can impersonate other users. If an administrator has an impersonator role, they can impersonate users and administrators. The impersonator has access to what the user can access in the system, including the same tools, user interface layout, etc. The instance records impersonator's activities on behalf of the impersonated user, but specifies that it was within the impersonation session.
Impersonate
To impersonate a user, complete the steps below:
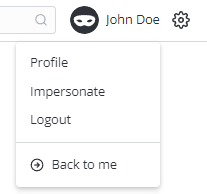
In the header, click your name or profile photo to open the user menu.
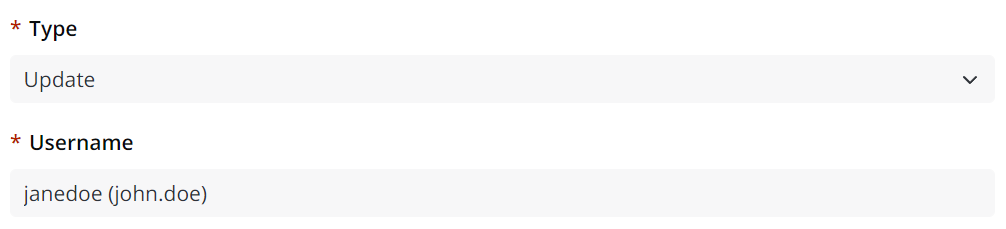
Select Impersonate to open the modal window.
Start typing the name of the user you need to impersonate. When the necessary user appears in the autosuggest, select it.
To return to your original login session, complete the following steps:
Click the name or profile photo to open the user menu.
Click Back to me.
Impersonation
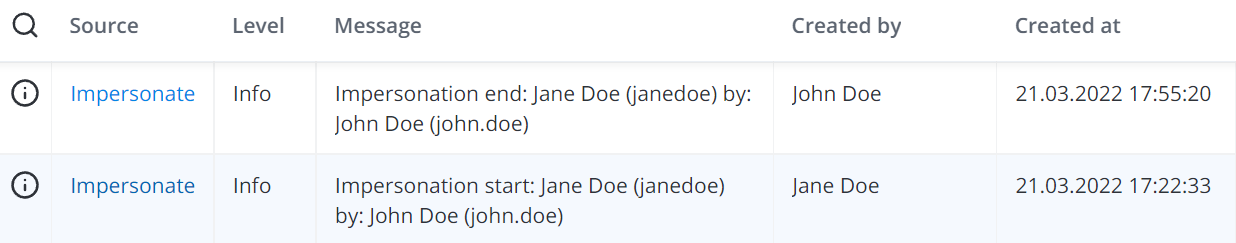
Every time a user personating another user, a related record appears in Main Log (sys_log). The format of the Message value in the record is as follows:
Impersonation {start|end}: <impersonated_user> by: <impersonator>
where both the impersonated user and impersonator are specified in the Display Name (login) format.
Both the Impersonation start and Impersonation end log records get created on behalf of the user whose account will be used for further actions:
Impersonation start record: Impersonated userImpersonation end record: Impersonator
See the screenshot below for an example:
impersonated users are registered in System Logs, like any other user activity.
Each log record resulting from an action of an impersonated user appears in as if it is done in a usual user session:
Main Log (sys_log)
History (sys_history)
Script Log (sys_log_exception)
Exception Log (sys_log_script)
Record Deletion Log (sys_record_deletion_log)
See the System Audit article for more details.
the impersonator's login follows the login of the impersonated user in brackets: